In an age of evolving and global security threats, Subrosa’s encrypted mobiles are specially designed for communication privacy. Here the company’s chief executive, Troy Harper, reveals how completely secure communication ecosystems can provide value to a broad range of organisations.
Q: How did your encrypted mobiles come about?
Subrosa’s partner is Secure Group, an encrypted communications solutions provider based in Canada and active across Europe. The founders of both companies made their names in mobile and encrypted solutions, and were very much on the ground as BlackBerry devices became popular. They saw BlackBerry’s vision – which essentially was to provide secure, encrypted email – and extend it. They wanted to create a properly secure mobile phone ecosystem. That was their starting premise.
Q: How does the technology work?
Our devices offer everything you’d expect from modern mobile phones however every aspect is encrypted. Just like BlackBerry devices, Subrosa’s phones provide encrypted email, but they also provide encrypted messaging, voice chat, push-to-talk messaging, video messaging, video calls and, on the hardware side, encrypted phone storage. The phone itself has multiple layers of encryption, meaning that all user information is secured all of the time, with nothing exposed.
Fundamentally what we’ve done is to question the security of our mobile devices at every step of the user journey. We start with the SIM card. We secure our own SIM cards to prevent malware and others type of unwanted software getting pushed out directly from SIM providers to phones without users knowing. We’ve also written all our own apps, including our encrypted chat and encrypted vault apps, to remove any chance of third-party monitoring or routing through servers, and to ensure there’s no spyware in our software.
Q: Which organisations stand to benefit most from using your encrypted mobiles?
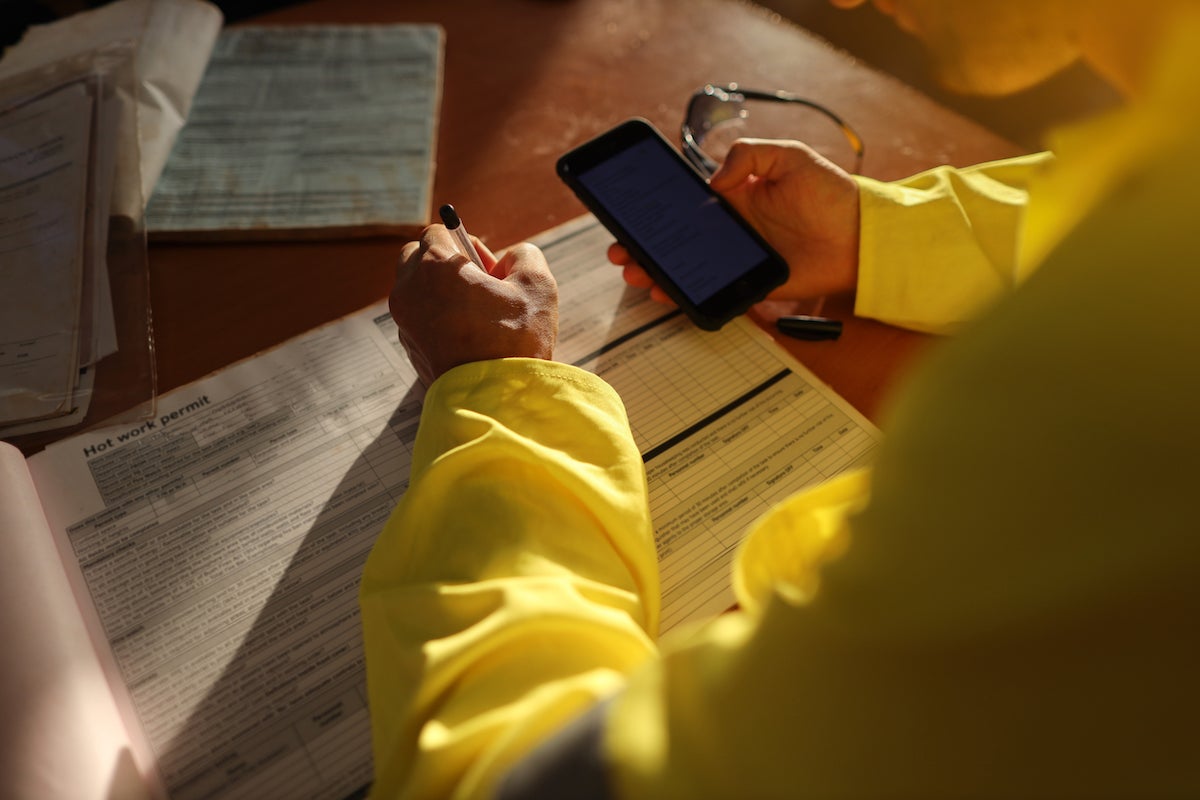
Our phones are ideal for senior executives who travel a lot and are looking to secure their communications while in foreign countries. We’re becoming more involved in the mining sector because of the specific profiles of most mining executives. They’re often travelling to areas where security is low, but where they need the ability to talk about highly sensitive subjects – like potential discoveries – that can impact share prices to the tune of hundreds of millions of dollars.
We have a broad range of clients in other industries too, and in government. Many of our users, particularly in the UK, are just private businesses that need secure communications. As we’ve developed our technology and thought more about what our products stand for, and what they truly offer, we’ve recognised an ever-growing number of potential use cases.
Q: What makes your encrypted mobiles unique compared to others on the market?
Our phones operate in a completely secure, closed network alongside your standard corporate communications. Essentially, the devices are hack proof. Nobody can steal your identity or phish your credentials.
Phishing attacks have become increasingly prevalent and sophisticated, and that’s set to continue. But our devices can actually prevent all phishing attacks, because once you carry out transactions via our secure phones, you’ll know for sure that your communications and payments will be going to the correct person, because it’s only their secure device that can communicate with yours. This level of security effectively shuts out the risk of phishing attacks. It’s extremely hard for hackers to get around that.
Our devices can be rolled out to all your vendors, who can then instruct any payment changes through their secure phones.
What makes us unique is the fact we go to the nth degree to truly secure the communications experience for customers. It opens up a range of broader uses for our devices that other products can’t do.
Q: What are Subrosa’s company values?
Subrosa is a can-do, solutions-based company. It’s not enough for us just to have great technology. We also want to communicate what our technology can do, in the clearest possible way, once it’s been implemented. When we provide our devices to customers, we help train them so they can get the most out of them.
We’re big on training and on customer support. There’s too much great technology out there that is sold and then isn’t set up properly, making it ineffectual. You see it a lot with firewall technology and anti-virus protection. We make sure that when our devices land, that they’re set up, they’re tested and they work. We’re really interested in making sure that our customers have the best possible experience when setting up their ecosystem. We make the experience seamless and supportive.
Q: What gets you excited about the projects you work on?
We get excited when we see our customers really getting to grips with our products, realising their true value, and using them in the way they’re meant to be used.
We consider a project successful not at the point that we receive positive feedback, but when we see that customers have truly embraced the technology, and are using it regularly. We’re excited when our technology is imbedded deeply within an organisation, and when individuals who may have been resistant to the new technology become comfortable with it, and eventually advocate for it. That’s what we love.


